We were exhibiting with Atola Insight Forensic at Enfuse and Techno Security conferences and received plenty of questions from people visiting our booth. Some of these questions were repeatedly asked, so sharing them and their corresponding answers in this blog makes sense. We do hope you find the information provided here helpful!
What is the maximum imaging speed?
You can always observe an actual imaging performance of 30 GB/min in Atola Insight Forensic v4.5 with a couple of Samsung 850 Pro solid-state drives used as source and target devices.
Why is Atola Insight Forensic better than competing products?
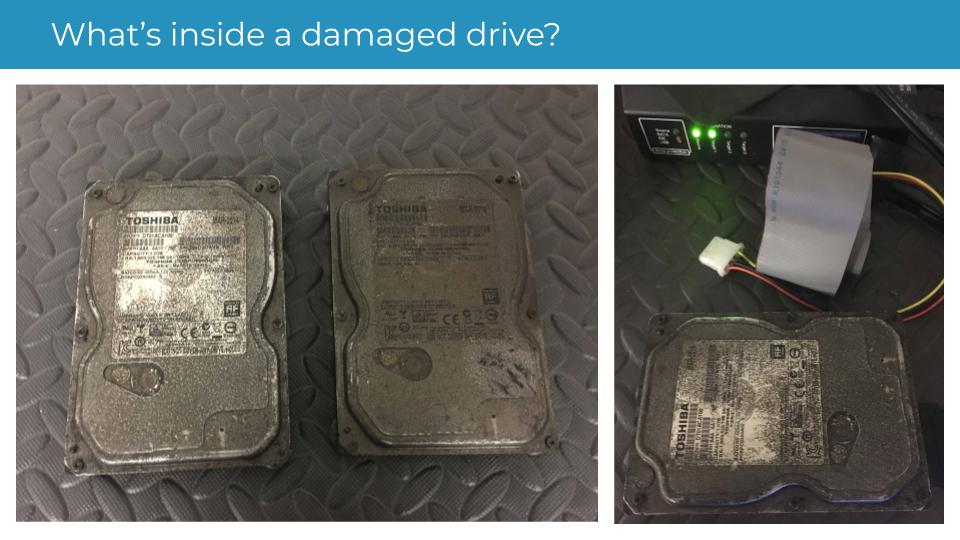
We produce the only solution that is specifically designed to support damaged media.
Our users usually begin with automatic diagnostics for an evidence drive. It takes a couple of minutes yet saves much of time and energy. It detects drive issues such as PCB instability, problems with motor, short circuit, firmware errors, degraded or even nonworking heads, and physical media surface damage. Afterward, you can make a decision on what to do next with the evidence drive.
Even if you work with severely damaged source device, the imaging engine enables you to:
- disable damaged heads
- automatically overcome much more serious problems than so-called ‘software bad sectors’
- track drive state before, during and after imaging
- have every imaging event logged in a forensically sound manner
Atola Insight has file recovery integrated with imaging. By browsing the target image directory tree, you can always see which source file sectors are bad sectors or even were read with the ReadLong ATA command (without ECC).
Last but not least, Atola Insight Forensic can clear any unknown ATA password from the hard disk drive in just a minute.
What image formats can be used for target files?
Atola Insight Forensic supports imaging to three image file types:
- growing files: *.img
- preallocated files: *.imgp
- E01 files: *.e01
The first two are raw files, bit-to-bit source copies. The 3rd target file type is E01 (Encase). It can be either compressed or not. Imaging to non-compressed E01 is several times faster and does not depend on CPU speed and core count.
How exactly does Atola Insight imaging process cope with damaged drives?
We have two goals here when dealing with severely damaged source drives:
1) Get as much data as possible
2) Decrease the number of failed read attempts to finish imaging with a still-alive evidence drive
Atola Insight Forensic uses a fast imaging map, thereby enabling us to run the whole process in multiple passes. The tool uses large blocks with short time-outs on the first few passes and then smaller blocks with longer time-outs on the last pass to image the tough areas. This provides the best possible results in the shortest amount of time
Atola Insight’s ability to disable damaged heads can just save your evidence! Other imagers merely kill the drive during imaging. Imagine having seven of eight good heads. You can just image with all of them except the damaged one. Afterward, you can begin analysis of 87% of the acquired data and at the same time try to replace the damaged head. A physical head swap is always a risky challenge.
The imaging engine contains many automatic rules. For example, it resets or power-cycles the source when the source drive freezes. It can apply a reverse imaging direction in particular cases. Here is what is useful when dealing with damaged evidence: Two imaging reports are created before and after the process. Both include not only imaging information but also SMART tables, thus enabling you to see what happened to the source drive during the process.
You claim you have the fastest forensic imager. How much forensic is it?
All source ports are write-protected:
- SATA
- IDE
- USB
- SAS and PCIe as extension modules
On top of that, overcurrent protection detects when the hard drive draws abnormal current and stops the hard drive to prevent any further damage.
Every action in Atola Insight is followed by automatically created case reports. The case management system gets a new report even if you physically flip the DiskSense unit’s write protection switch. Additionally, every case report includes mandatory information about the device, DiskSense unit, current PC, OS, and user.
- Atola TaskForce 2023.4.2 stability update - August 7, 2023
- Wipe multiple drives in Atola Insight Forensic 5.2 - May 26, 2022
- Logical imaging in TaskForce 2022.4 - April 11, 2022